Portal:Internet
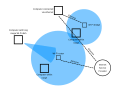
The Internet PortalThe Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. The Internet is the single largest network of networks (or "internet") that consists of private, public, academic, business, and government networks of local to global scope, linked by a broad array of electronic, wireless, and optical networking technologies. The Internet carries a vast range of information resources and services, such as the interlinked hypertext documents and applications of the World Wide Web (WWW), electronic mail, telephony, and file sharing. The origins of the Internet date back to the development of packet switching and research commissioned by the United States Department of Defense in the late 1960s to enable time-sharing of computers. The primary precursor network, the ARPANET, initially served as a backbone for the interconnection of regional academic and military networks in the 1970s to enable resource sharing. The funding of the National Science Foundation Network as a new backbone in the 1980s, as well as private funding for other commercial extensions, led to worldwide participation in the development of new networking technologies, and the merger of many networks. The linking of commercial networks and enterprises by the early 1990s marked the beginning of the transition to the modern Internet, and generated a sustained exponential growth as generations of institutional, personal, and mobile computers were connected to the network. Although the Internet was widely used by academia in the 1980s, commercialization incorporated its services and technologies into virtually every aspect of modern life. (Full article...) Selected article
YouTube is a video sharing website where users can upload, view and share video clips. YouTube was created in mid-February 2005 by three former PayPal employees. The San Bruno-based service uses Adobe Flash technology to display a wide variety of video content, including movie clips, TV clips and music videos, as well as amateur content such as videoblogging and short original videos. In October 2006, Google Inc. announced that it had reached a deal to acquire the company for US$1.65 billion in Google stock. The deal closed on November 13, 2006. Unregistered users can watch most videos on the site, while registered users are permitted to upload an unlimited number of videos. Some videos are available only to users of age 18 or older (e.g. videos containing potentially offensive content). The uploading of pornography or videos containing nudity is prohibited. Related videos, determined by title and tags, appear onscreen to the right of a given video. In YouTube's second year, functions were added to enhance user ability to post video 'responses' and subscribe to content feeds. Few statistics are publicly available regarding the number of videos on YouTube. However, in July 2006 the company revealed that more than 100 million videos were being watched every day, and 2.5 billion videos were watched in June 2006.
Selected pictureLeet (written 31337, 1337, and l33t), or Leetspeak, is a written argot used primarily on the Internet, which uses various combinations of alphanumerics to replace Latinate letters. The term is derived from the word "elite", and the usage it describes is a specialized form of shorthand. News
Wikinews Internet portal
WikiProjects
Did you know (auto-generated) -
Selected biography
Danah Michele Boyd (or danah boyd, born Danah Michele Mattas in 1977), is an American academic, researcher, and blogger best known for media appearances where she speaks about social networking sites such as Friendster and MySpace. Since 2003, she and her research have been quoted on the subject of social networking in dozens of different articles in media sources such as NPR, Wired, MSNBC, USA Today, Newsweek and The O'Reilly Factor. She was also the subject of a major profile in The New York Times in 2003 and the Financial Times in 2006. She initially studied computer science at Brown University where she worked with Andy van Dam, and then pursued her Master's Degree in sociable media with Judith Donath at the MIT Media Lab. She advanced to Ph.D. candidacy in the UC Berkeley School of Information in 2006, and will be a non-resident fellow at the Berkman Center for Internet & Society for the 2007-2008 academic year.
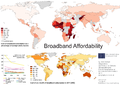
General images -The following are images from various internet-related articles on Wikipedia.
Selected quoteMore Did you know...
Main topicsHTTP Strict Transport Security (HSTS) is a policy mechanism that helps to protect websites against man-in-the-middle attacks such as protocol downgrade attacks[1] and cookie hijacking. It allows web servers to declare that web browsers (or other complying user agents) should automatically interact with it using only HTTPS connections, which provide Transport Layer Security (TLS/SSL), unlike the insecure HTTP used alone. HSTS is an IETF standards track protocol and is specified in RFC 6797. The HSTS Policy is communicated by the server to the user agent via an HTTP response header field named " The protection only applies after a user has visited the site at least once, relying on the principle of "trust on first use". The way this protection works is that a user entering or selecting a URL to the site that specifies HTTP, will automatically upgrade to HTTPS, without making an HTTP request, which prevents the HTTP man-in-the-middle attack from occurring. Specification historyThe HSTS specification was published as RFC 6797 on 19 November 2012 after being approved on 2 October 2012 by the IESG for publication as a Proposed Standard RFC.[3] The authors originally submitted it as an Internet Draft on 17 June 2010. With the conversion to an Internet Draft, the specification name was altered from "Strict Transport Security" (STS) to "HTTP Strict Transport Security", because the specification applies only to HTTP.[4] The HTTP response header field defined in the HSTS specification however remains named "Strict-Transport-Security". The last so-called "community version" of the then-named "STS" specification was published on 18 December 2009, with revisions based on community feedback.[5] The original draft specification by Jeff Hodges from PayPal, Collin Jackson, and Adam Barth was published on 18 September 2009.[6] The HSTS specification is based on original work by Jackson and Barth as described in their paper "ForceHTTPS: Protecting High-Security Web Sites from Network Attacks".[7] Additionally, HSTS is the realization of one facet of an overall vision for improving web security, put forward by Jeff Hodges and Andy Steingruebl in their 2010 paper The Need for Coherent Web Security Policy Framework(s).[8] HSTS mechanism overviewA server implements an HSTS policy by supplying a header over an HTTPS connection (HSTS headers over HTTP are ignored).[1] For example, a server could send a header such that future requests to the domain for the next year (max-age is specified in seconds; 31,536,000 is equal to one non-leap year) use only HTTPS: When a web application issues HSTS Policy to user agents, conformant user agents behave as follows (RFC 6797):[9]
The HSTS Policy helps protect web application users against some passive (eavesdropping) and active network attacks.[10] A man-in-the-middle attacker has a greatly reduced ability to intercept requests and responses between a user and a web application server while the user's browser has HSTS Policy in effect for that web application. ApplicabilityThe most important security vulnerability that HSTS can fix is SSL-stripping man-in-the-middle attacks, first publicly introduced by Moxie Marlinspike in his 2009 BlackHat Federal talk "New Tricks For Defeating SSL In Practice".[11][12] The SSL (and TLS) stripping attack works by transparently converting a secure HTTPS connection into a plain HTTP connection. The user can see that the connection is insecure, but crucially there is no way of knowing whether the connection should be secure. At the time of Marlinspike's talk, many websites did not use TLS/SSL, therefore there was no way of knowing (without prior knowledge) whether the use of plain HTTP was due to an attack, or simply because the website had not implemented TLS/SSL. Additionally, no warnings are presented to the user during the downgrade process, making the attack fairly subtle to all but the most vigilant. Marlinspike's sslstrip tool fully automates the attack.[citation needed] HSTS addresses this problem[10] by informing the browser that connections to the site should always use TLS/SSL. The HSTS header can be stripped by the attacker if this is the user's first visit. Google Chrome, Mozilla Firefox, Internet Explorer and Microsoft Edge attempt to limit this problem by including a "pre-loaded" list of HSTS sites.[13][14][15] Unfortunately this solution cannot scale to include all websites on the internet. See limitations, below. HSTS can also help to prevent having one's cookie-based website login credentials stolen by widely available tools such as Firesheep.[16] Because HSTS is time limited, it is sensitive to attacks involving shifting the victim's computer time e.g. using false NTP packets.[17] LimitationsThe initial request remains unprotected from active attacks if it uses an insecure protocol such as plain HTTP or if the URI for the initial request was obtained over an insecure channel.[18] The same applies to the first request after the activity period specified in the advertised HSTS Policy Junade Ali has noted that HSTS is ineffective against the use of phony domains; by using DNS-based attacks, it is possible for a man-in-the-middle interceptor to serve traffic from an artificial domain which is not on the HSTS Preload list,[21] this can be made possible by DNS Spoofing Attacks,[22] or simply a domain name that misleadingly resembles the real domain name such as www.example.org instead of www.example.com. Even with an HSTS preloaded list, HSTS cannot prevent advanced attacks against TLS itself, such as the BEAST or CRIME attacks introduced by Juliano Rizzo and Thai Duong. Attacks against TLS itself are orthogonal to HSTS policy enforcement. Neither can it protect against attacks on the server - if someone compromises it, it will happily serve any content over TLS. See RFC 6797 for a discussion of overall HSTS security considerations. Privacy issuesHSTS can be used to near-indelibly tag visiting browsers with recoverable identifying data (supercookies) which can persist in and out of browser "incognito" privacy modes. By creating a web page that makes multiple HTTP requests to selected domains, for example, if twenty browser requests to twenty different domains are used, theoretically over one million visitors can be distinguished (220) due to the resulting requests arriving via HTTP vs. HTTPS; the latter being the previously recorded binary "bits" established earlier via HSTS headers.[23] Browser support
Deployment best practicesDepending on the actual deployment there are certain threats (e.g. cookie injection attacks) that can be avoided by following best practices.
See also
References
External links
Featured contentCategoriesSelect [►] to view subcategories
Related portalsThings you can do
Associated WikimediaThe following Wikimedia Foundation sister projects provide more on this subject:
Wikipedia's portals |






















_(page_62_crop).jpg/120px-Get_on_the_%27Net%27%2C_State_Magazine_1997-03-_Iss_403_(IA_sim_state-magazine_1997-03_403)_(page_62_crop).jpg)







